Is Your Digital Life More Vulnerable Than You Think? A Friendly Guide to How AI cybersecurity defense systems Guard Your Everyday Life
Have you noticed that online scams are starting to sound a bit too “real” lately?

Recently, you may have started to see a new trend with scams on social media or chat groups . That is concerning: scams have evolved beyond just “Nigerian princes” and poorly written emails. We’re now hearing about people receiving calls from a “boss” who has their voice replicated perfectly, or receiving job documents.They look completely legit only to click on the document and your entire screen goes dark.
- Have you noticed that online scams are starting to sound a bit too “real” lately?
- How do AI-powered cybersecurity systems manage to stay awake when everyone else is sleeping?
- Can traditional firewalls really survive when hackers use AI-based intrusion detection systems (IDS) tactics?
- If AI is so powerful, does it mean our IT teams can go on a long holiday?
- How can we protect ourselves against the hidden traps of AI cybersecurity defense systems?
The reality of it is that hackers have upgraded their ways of executing their attacks by using Artificial Intelligence (AI), which will facilitate the speed and level of their attack. If we continue to rely solely on traditional methods of securing ourselves then we are attempting to stop a modern-day sports car using nothing more than a wooden fence. This is why people in the industry are starting to speak more about AI cybersecurity defense systems.
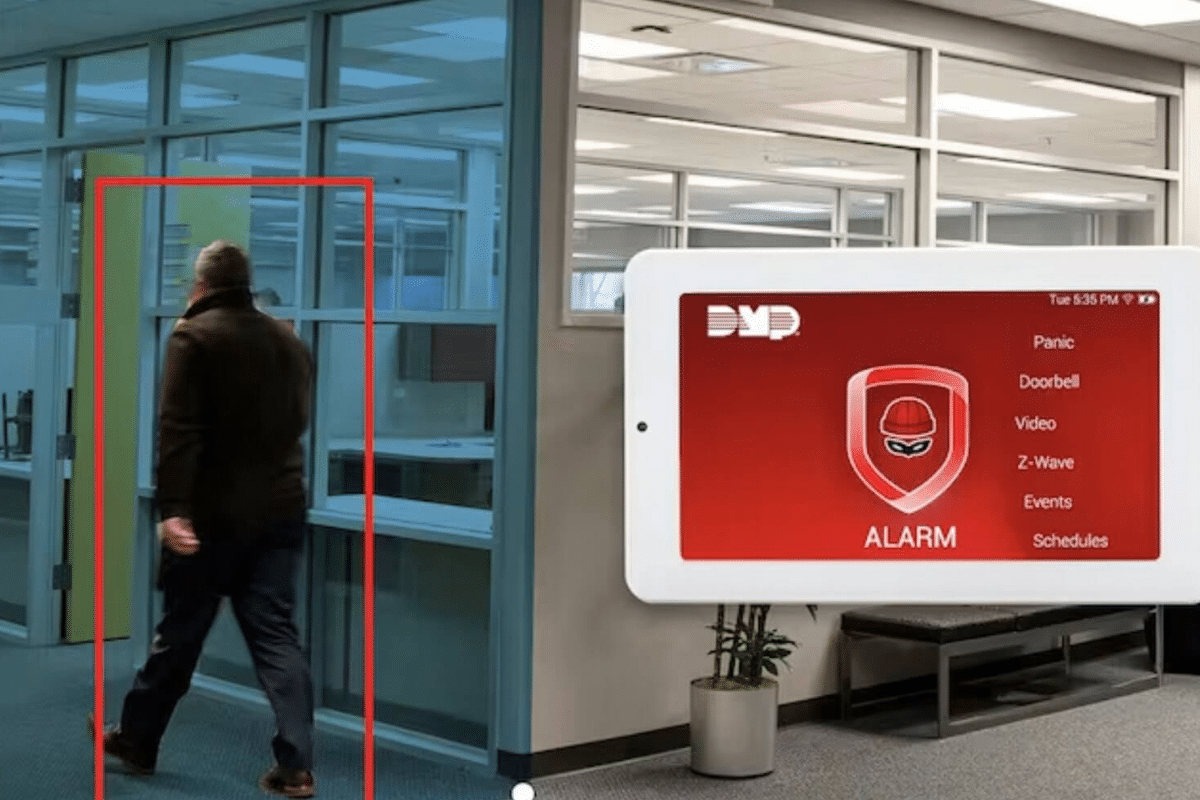
To illustrate this analogy: a traditional security system is like a guard that has a “blacklist” of people that are not allowed into the building. A person that isn’t on the list is allowed inside. But, if a thief comes in with a mask or has a new name, then the guard will become confused. With an AI-driven security system, think of it as an elite agent that does not just check an ID but also observes a person’s walk, their mannerisms and aura to make sure that nothing seems “off” with that person. If there is something that seems “off” with that person, the gates will lock immediately.
How do AI-powered cybersecurity systems manage to stay awake when everyone else is sleeping?
Cybersecurity is often thought of as a software solution that is installed once. But in reality it is a dynamic, ongoing struggle. For businesses and busy individuals, there are thousands of pieces of information entering and leaving their devices every moment of every day which no person could possibly monitor humanly. This is where AI cybersecurity defense systems come into play. Their best quality is that they never tire. While you could be awake and preparing a midnight snack to go along with your breakfast cereal, AI is processing enormous volumes of data in real time from all of those data points.
Diagram illustrating how anomaly detection algorithms identify cyber threats in real time. Here’s an example: when you access your banking app during normal hours from Petaling Jaya and spend RM200 on groceries, the system ascertains that this activity is “you”. However, when you access your bank account at 3 AM in the morning from a server in Eastern Europe for the purpose of spending RM50,000 on a Rolex, real-time threat intelligence allows AI to identify this logic error instantaneously (0.01 seconds). Therefore, instead of waiting for a human supervisor to wake up and respond to the attempted theft (by human effort) the AI freezes the transaction immediately. This demonstrates the type of proactive protection necessary today.
Can traditional firewalls really survive when hackers use AI-based intrusion detection systems (IDS) tactics?
AI is being used by hackers to create “mutating” viruses. Essentially an AI vs. AI battle. Before, traditional viruses were like common colds. They had a cure as soon as a doctor (your antivirus) discovered there was one. Modern-day malware, however, is like a shape-shifting virus—the code changes whenever it tries to access another computer.
As a result, organizations can no longer use hard (i.e., rigid) firewalls to protect themselves from malware. Instead, these organizations need to replace their hardwired firewalls with AI-based Intruder Detection Systems (IDS). That can monitor everything that’s going on inside their networks 24/7. The IDSs will use behavioral analysis security systems. Meaning that they are smart and analyze the behavior of files once they enter the network. When a file enters a system and tries to change the system settings or copy the customer database, the AI-moderated malware detection systems will identify these files as malware and will stop them before they spread.
In addition, there is a move towards zero-trust security architecture based on AI. Several years ago, we thought of a person being inside your office Wi-Fi as being considered a friend. Today, we think of every person on your office Wi-Fi as needing verification to access your network. This may sound unreasonable. However, in a world where the digital asset is worth more than the physical asset, this is the only way to ensure safety.
Detection is Good, Response is Better
The real power of AI cybersecurity defense systems isn’t just spotting a hacker; it’s the speed of isolation. In the time it takes a human to read an alert, AI has already quarantined the threat, preventing a single leak from becoming a total shutdown.
If AI is so powerful, does it mean our IT teams can go on a long holiday?
Business owners are frequently curious about the role of networking security automation. Oftentimes when business owners first discover security network automation, they have the same question: “Wow, if a machine can complete the entire process without human involvement, will I need to employ someone”? There seems to be some misunderstanding here. While AI has been developed to be extremely fast at processing information, the ever-evolving technologies it uses still require human oversight related to big-picture strategy. Therefore, although AI will ultimately assume the majority of repetitive, tedious and high-volume tasks (e.g., automated incident response systems), it will leave us with a very small percentage of actual, complex, targeted attacks (1%) for the decision-makers of those industries.
This supports the idea in the medical field, where a robotic device may help stabilize the surgeon’s hand or provide real-time images of the patient’s conditions. However, the surgeon makes the critical decisions with all available input from other human sources. Therefore, BidaTech AI, along with the additional cybersecurity automation tools being introduced. It served as critical pieces of the administrative and strategic support one requires for a complete understanding of their organization and that the logical processing of the machine drives their organization toward its goals.
How can we protect ourselves against the hidden traps of AI cybersecurity defense systems?
The principles of adaptive cyber defense apply equally to all businesses regardless of size and scale. The first thing to remember is that phishing emails have become more difficult to identify than ever. Hackers are using AI phishing detection tools in reverse to figure out how to get through the most common filters. If you have an email with a link in it that looks strange, don’t click it. If a call you receive from your bank seems urgent or important, hang up and call back using the official phone number.
Diagram illustrating multiple layers surrounding endpoint protection AI-based solutions. Small businesses are not required to build their own server rooms. There are cloud service providers that offer endpoint protection AI-based solutions as part of their offerings. There are many platforms that use AI machine learning algorithms to filter out 99.9% of all spam emails before they ever reach your inbox. Today, cybersecurity is a necessity rather than an optional feature for the average small business. By keeping your wits and letting artificial intelligence do the majority of the work, we will all have a safer online environment to conduct our business and to connect with one another.










